GitHub - mikeroyal/Self-Hosting-Guide: Self-Hosting Guide. Learn all about locally hosting (on premises & private web servers) and managing software applications by yourself or your organization. Including ChatGPT, WireGuard, Automation, Home Assistant ...

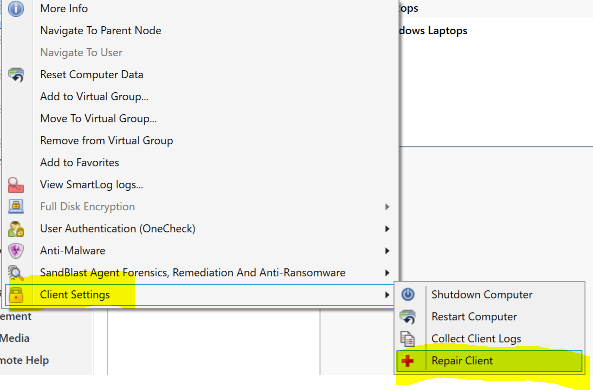
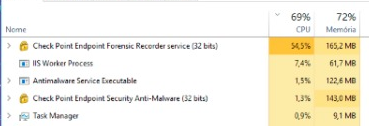
windows - 100% CPU usage when running WSL2 in Check Point Endpoint Security VPN installed environment - Super User

Lee Reiber - Mobile Forensic Investigations - A Guide To Evidence Collection, Analysis, and Presentation, Second Edition-McGraw-Hill Education (2019) | PDF | Computer Forensics | Digital Forensics

US9209995B2 - Presence status notification from digital endpoint devices through a multi-services gateway device at the user premises - Google Patents