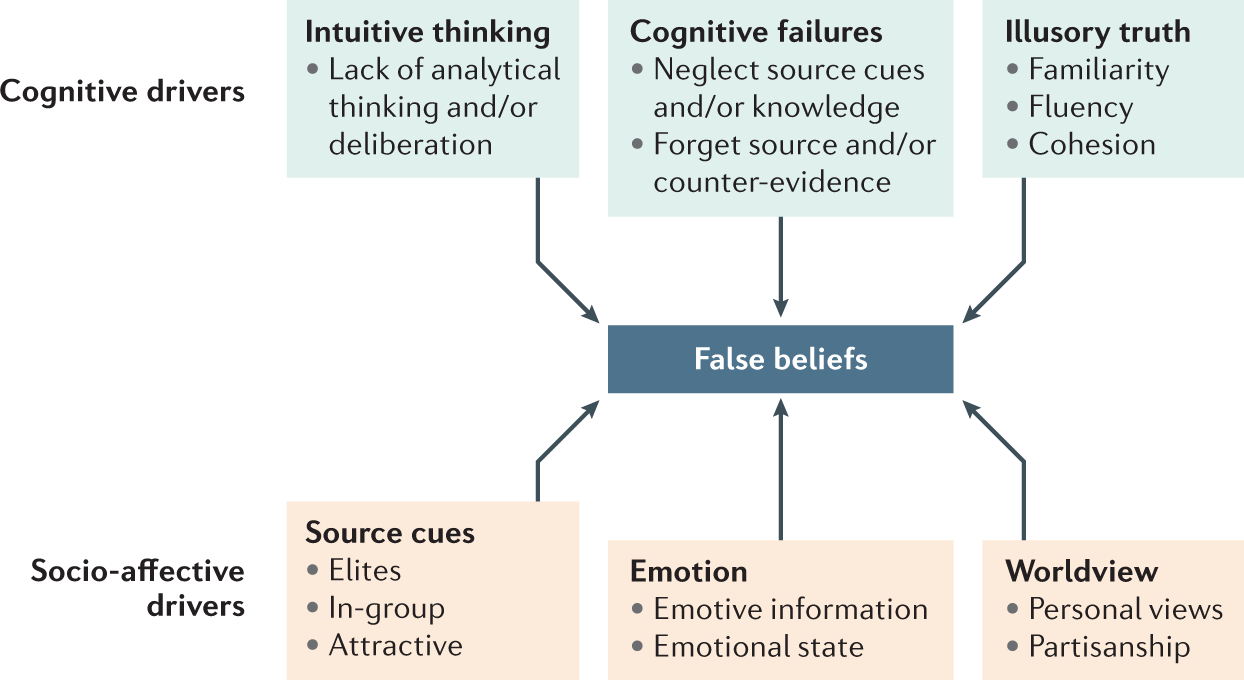
The psychological drivers of misinformation belief and its resistance to correction | Nature Reviews Psychology

The Practical Psychic Self-Defense Handbook: A Survival Guide: Bruce, Robert: 9781571746399: Amazon.com: Books
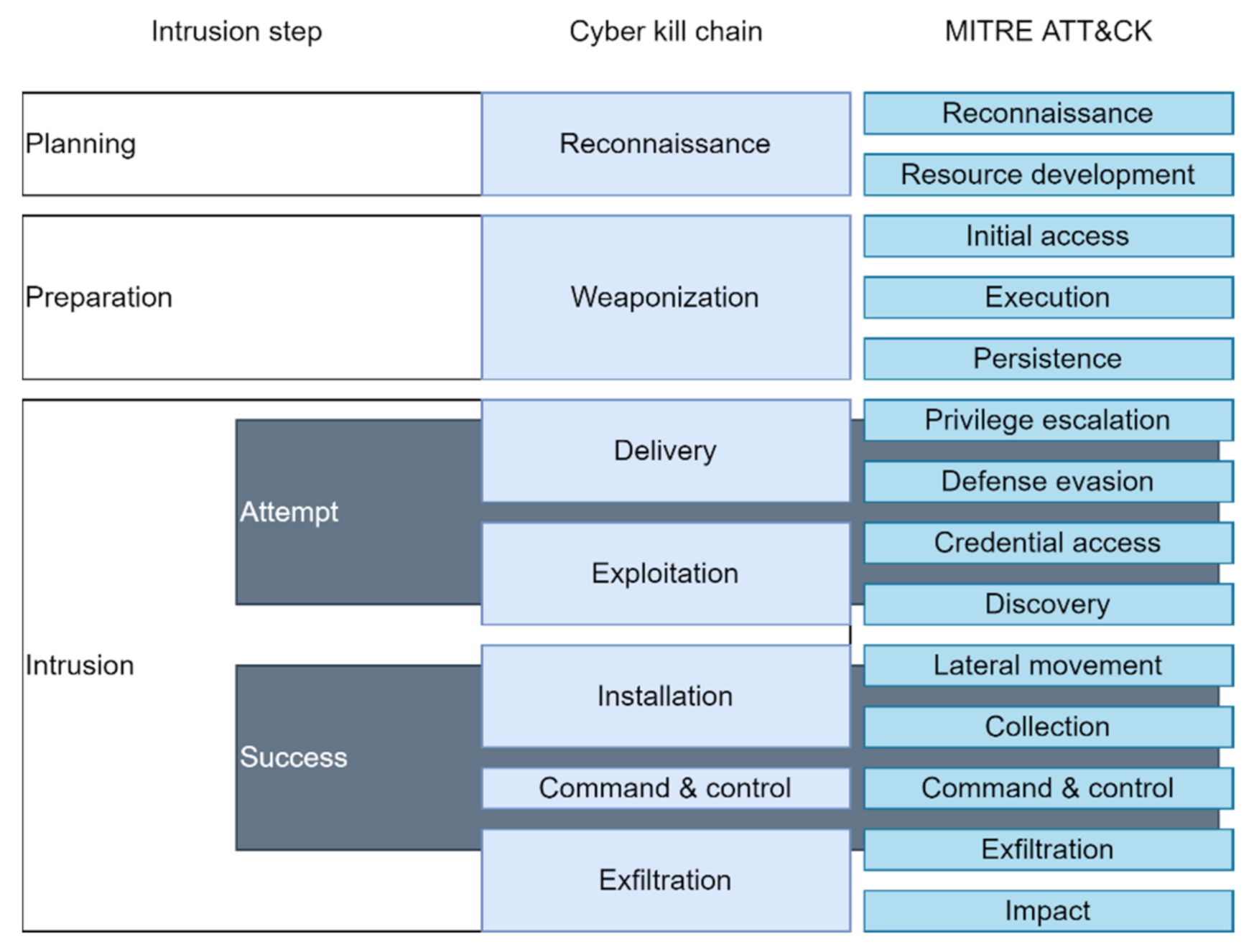
Sensors | Free Full-Text | Cyberattack Models for Ship Equipment Based on the MITRE ATT&CK Framework

The Chain Home Early Warning Radar System: A Case Study in Defense Innovation > National Defense University Press > News Article View
Check Point Research conducts Initial Security Analysis of ChatGPT4, Highlighting Potential Scenarios For Accelerated Cybercrime - Check Point Software
The UNESCO training manual for the protection of the underwater cultural heritage in Latin America and the Caribbean


![Technology Trends in 2022 – Keeping Up [Full Book for Managers] Technology Trends in 2022 – Keeping Up [Full Book for Managers]](https://www.freecodecamp.org/news/content/images/2022/05/bohdan-orlov-Buwi_A04F6k-unsplash.jpg)



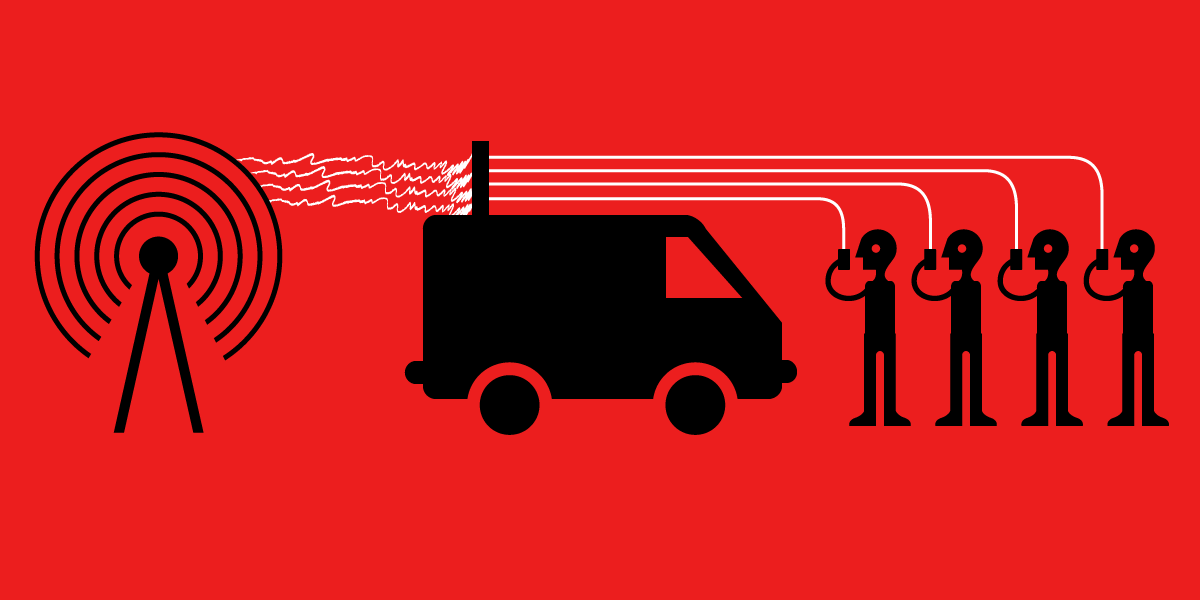
![Inside Radio: An Attack And Defense Guide [PDF] [4223clofej90] Inside Radio: An Attack And Defense Guide [PDF] [4223clofej90]](https://vdoc.pub/img/crop/300x300/7h70qulend40.jpg)